Download our free SNMP White Paper. Featuring SNMP Expert Marshall DenHartog.
This guidebook has been created to give you the information you need to successfully implement SNMP-based alarm monitoring in your network.
1-800-693-0351
Have a specific question? Ask our team of expert engineers and get a specific answer!
Sign up for the next DPS Factory Training!

Whether you're new to our equipment or you've used it for years, DPS factory training is the best way to get more from your monitoring.
Reserve Your Seat Today(This information is a small section from our full SNMP Tutorial PDF.)
The Simple Network Management Protocol (SNMP) is an Internet Standard protocol that is based on the manager/agent model with a simple request/response format. The network manager issues a request and the managed agents will send responses in return.
Currently, there are three major SNMP versions: SNMPv1, SNMPv2c, and SNMPv3.
Understanding these versions is crucial for effective network management, as each iteration introduces different features and improvements.
SNMP is a protocol that enables the exchange of management information between network devices and a network management system (NMS). It operates on the application layer of the TCP/IP protocol suite and uses a client-server architecture. SNMP allows network administrators to query and modify parameters on SNMP-enabled devices, as well as receive traps, notifications, or information from those devices.
Simplified Management: SNMP provides a standardized approach to managing diverse network devices, allowing for centralized monitoring and control.
Real-time Monitoring: It allows administrators to monitor network performance metrics, such as bandwidth utilization, CPU usage, and interface status, in real-time.
Proactive Issue Detection: With SNMP, administrators can set up alerts and notifications to be informed of any issues or anomalies on network devices, enabling prompt action to address them.
Scalability: SNMP is scalable and can handle large networks with a high number of devices, making it suitable for both small and large-scale network environments.
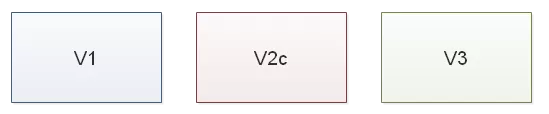
These different generations of SNMP have created a definite fracturing of what was once a simple architecture. Now, you have to consider the multi-generational SNMP versions you have in play and consider mediation devices to convert older SNMP to the newer version.
By utilizing SNMP monitoring tools, network administrators can leverage the power of SNMP to efficiently manage their network infrastructure, troubleshoot issues, and optimize performance. These tools provide graphical interfaces, comprehensive reporting, and automation capabilities to streamline network management tasks and enhance overall network reliability.
It is important that you are able to make informed decisions when it comes to your system communication methods. This is why we'll dive into these SNMP versions and learn the main differences between them.
SNMPv1 is the first version of SNMP. It's easy to set up, as it only requires a plain text community.
Although it accomplished its goal of being an open, standard protocol, it was found to be lacking in key areas for certain managing applications. For example, it only supports 32-bit counters and has poor security features - a community string is the only security method in the SNMPv1.
Later versions have addressed many of these problems. Smaller RTUs commonly support SNMPv1.
Protocol Operations in SNMPv1
GET: Retrieve information from a device.
GETNEXT: Obtain the next piece of data in a sequence.
SET: Modify configuration settings.
TRAP: Receive alerts from devices.
Designed in 1993, SNMPv2c (where c stands for community) is a sub-version of SNMPv2.
The Get, GetNext, and Set operations used in SNMPv1 are identical as those used in SNMPv2c. However, SNMPv2c's key advantage over previous versions is the Inform command. Unlike Traps, which are simply received by a manager, Informs are positively acknowledged with a response message. If a manager does not reply to an Inform, the SNMP agent will resend the Inform.
Additional Protocol Operations in SNMPv2c
GETBULK: Efficiently retrieve large amounts of data.
INFORM: Receive acknowledgment for messages sent.
SNMPv2 Trap: Enhanced trap messages with additional information.
Other advantages include:
Improved error handling
Improved SET commands
SNMPv2 security, just like for SNMPv1, comes into the form of community strings. This is a password that your devices will need to able allowed to talk to each other and transfer information when SNMP requests occur.
Also, keep in mind that not all devices are SNMPv2c compliant, so your SNMP manager should be downward compatible with SNMPv1 devices. You can also use an SNMPv3 mediation device to ensure compatibility with earlier versions.
When considering compatibility for SNMP versions, it's important to note the following:
SNMPv1: This version is widely supported across numerous devices, making it a reliable choice for basic network management tasks.
SNMPv2c: It is also widely supported and provides compatibility with SNMPv1, facilitating a smooth transition for networks upgrading from older systems. However, check whether your devices support SNMPv2c natively, as some may not.
SNMPv3: Known for its enhanced security features, SNMPv3 is widely supported across modern devices. It can integrate with previous versions using mediation devices, ensuring secure and seamless compatibility.
By understanding these compatibility aspects, you can make informed decisions about which SNMP version best suits your network needs and ensure your SNMP manager or devices are equipped to handle the required protocol versions.
SNMPv3 is the newest SNMP version. Its management framework features primarily involve enhanced security.
The SNMPv3 architecture introduces the User-based Security Model (USM) for message security and the View-based Access Control Model (VACM) for access control.
SNMPv3 supports the SNMP "Engine ID" Identifier, which uniquely identifies each SNMP entity. Conflicts can occur if two entities have duplicate EngineID's. The EngineID is used to generate the key for authenticated messages.
Protocol Operations in SNMPv3
GET: Retrieve device information.
GETNEXT: Access subsequent data.
SET: Update device configurations.
TRAP: Receive and handle alerts.
SNMP v3 security models come primarily in 2 forms: authentication and encrypting.
The SNMPv3 protocol also facilitates the remote configuration of the SNMP agents. It is defined by RFC 1905, RFC 1906, RFC 3411, RFC 3412, RFC 3414, RFC 3415.
The NetGuardian 832A G5 is one example of an RTU that supports SNMPv3.
The first version of SNMP to offer user-based access was SNMPv3. This was a game-changer in terms of network security because it introduced features like user authentication and encryption - tools that weren't available in SNMPv1 or SNMPv2c.
With SNMPv3's User-Based Security Model (USM), network admins can control access based on who the user is. This means you get not only the benefits of monitoring and managing your devices, but also the security of knowing that only verified users are accessing your network, with data encrypted along the way. SNMPv3 is a big step up from the more open, less secure SNMP versions that came before.
SNMP plays a critical role in monitoring devices like printers, network-attached storage (NAS), and uninterruptible power supplies (UPS). SNMP helps administrators track device performance, collect data on device status, and identify problems before they escalate. By using SNMP for monitoring devices like these, you can be confident in your ability to have continuous uptime, optimize performance, and proactively address issues.
SNMP allows administrators to monitor printers for key metrics like toner levels, paper jams, and error messages. This helps IT teams remotely diagnose and resolve issues before users even notice. SNMP traps can notify admins of critical events such as paper tray shortages or failed print jobs, making sure there are minimal disruptions in printing services. Integrating SNMP into printer management enables efficient maintenance scheduling, reducing downtime and service interruptions.
For NAS devices, SNMP enables detailed monitoring of storage capacity, disk health, and overall system performance. Administrators can track important metrics like disk space utilization, RAID status, and network throughput. With SNMP monitoring, alerts are sent when storage limits are approaching, or if there are disk failures. This allows for prompt responses to prevent data loss or performance degradation. This proactive approach upholds that NAS systems run smoothly and remain available for users.
UPS monitoring through SNMP provides real-time data on variables such as battery status, load capacity, and runtime. In the event of power outages or surges, SNMP can send immediate alerts. These rapid alerts allow administrators to initiate controlled shutdowns or take protective measures. SNMP also helps monitor long-term battery health, alerting users when it's time for battery replacements, thus avoiding unexpected failures and maintaining operational continuity.
If now you have to use only secure/encrypted SNMPv3, you need a way to avoid replacing all of your current v1/v2c SNMP network devices. A conversion device allows you to do that. Talk to your vendor about that, this way you can keep your older gear and add SNMPv3 security.
The Fast Track Introduction to SNMP is a quick, 12-page introduction to SNMP. You'll learn about traps, message formats, message processing, MIB objects, SNMPv3 security and administration, and other fundamental SNMP concepts.
At DPS, we're totally focused on remote monitoring, including SNMP protocol. We've worked on thousands of projects that involve SNMP in one form or another.
That experience means that we have SNMP experts on staff. Send us a quick online message (or just give us a call) and we'll answer any SNMP question you have.
Next Page: Field-Tested, Proven SNMP Mediation
All DPS Telecom products include comprehensive technical support. If you've purchased one of our products and are encountering any kind of issue, contact DPS Tech Support today at 559-454-1600.
At DPS Telecom, the representative who answers your call isn't an intern reading from a script. DPS Tech Support representatives are engineers who contribute to product development. And, if your problem requires additional expertise, the DPS Engineering Department that designed your product is right down the hall.
Help us connect you to the right engineer by filling out this quick questionnaire. Simply leave your contact information to get started, and we'll call you back. Most preliminary discussions are about 15 minutes, and afterward, we'll send you a custom application diagram of a recommended solution that'll make it easier to justify your project to management.