Check out our White Paper Series!
A complete library of helpful advice and survival guides for every aspect of system monitoring and control.
1-800-693-0351
Have a specific question? Ask our team of expert engineers and get a specific answer!
Sign up for the next DPS Factory Training!

Whether you're new to our equipment or you've used it for years, DPS factory training is the best way to get more from your monitoring.
Reserve Your Seat TodayAre you new to the network management world? Do you have SNMP equipment deployed at your remote sites?
Especially if you are just beginning to learn the principles of the SNMP protocol, effectively using a MIB browser to collect and configure information in your remote sites can be incredibly helpful.
Let's go over the basics of the SNMP protocol, MIB, and how exactly an SNMP MIB browser can be useful for you.
Simple Network Management Protocol (SNMP) is nothing more than a standard language that computers use to control each other and report important information in real-time.
Since its creation in 1988, as a short-term solution to manage elements in the growing Internet and other attached networks, SNMP has achieved widespread acceptance. Its advantage today is that a very large number of devices support it, enabling them to work together.
SNMP was derived from its predecessor SGMP (Simple Gateway Management Protocol) and was intended to be replaced by a solution based on the CMIS/CMIP (Common Management Information Service/Protocol) architecture. This long-term solution, however, never received the widespread of SNMP.
Part of why SNMP has reached such wide adoption is due to the fact that it's an open standard. This means that this protocol allows devices from different vendors to communicate with one another.
While there are widely accepted standards, there's no governing body that controls how SNMP can and cannot be used, or declares and set rules for how messages are created and processed, making it extremely flexible and unable to be made obsolete by a singular vendor going out of business.
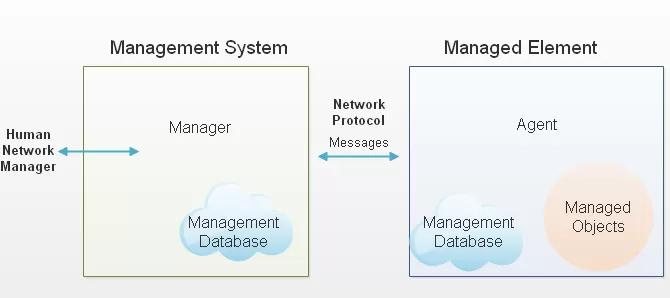
SNMP is based on the manager/agent model that consists of a manager, agent, a database of management information, managed objects and the network protocol. The manager provides the interface between the human network manager and the management system. The agent provides the interface between the manager and the physical device(s) being managed.
The SNMP protocol uses five basic message types to communicate between the manager and the agent:
The Get and GetNext messages allow the manager to request information for a specific variable. The agent, upon receiving a Get or GetNext message, will issue a GetResponse message to the manager with either the information requested or an error indication as to why the request can't be processed.
A Set message allows the manager to request a change be made to the value of a specific variable in the case of an alarm remote that will operate a relay. The agent will then respond with a GetResponse message indicating the change has been made or an error indication as to why the change can't be made.
SNMP Traps allow the agent to spontaneously inform the manager of an "important" event.
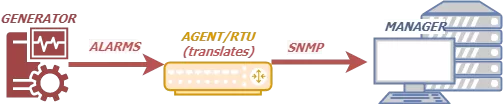
As you can see, most of the messages (Get, GetNext, and Set) are only issued by the SNMP manager. Because the Trap message is the only message capable of being initiated by an agent, it's the message that we use here for our RTUs to report alarms. This notifies the SNMP manager as soon as an alarm condition occurs, instead of waiting for the SNMP manager to ask.
The small number of commands used is only one of the reasons SNMP is simple. The other simplifying aspect is its reliance on an unsupervised or connectionless communication link.
This simplicity has led directly to its widespread use, specifically in the Internet Network Management Framework. Within this framework, it's considered robust because of the independence of the managers from the agents. This means that, if an agent fails, the manager will continue to function, or vice versa.
Now that we've talked about the basics of the SNMP protocol, it's important to dive in a little bit further into the MIB principles.
The SNMP manager and the SNMP agent use a Management Information Base - aka MIB - and a relatively small set of commands to exchange information.
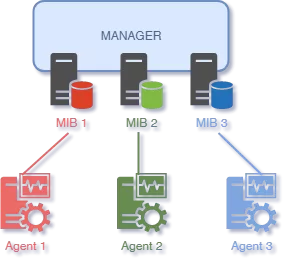
A MIB is a formatted text file that lists all of the data objects used by a particular piece of equipment. When you buy a device that uses SNMP (for example, a managed switch), you'll tell it to send messages to your central SNMP manager. But there are tens of thousands of different SNMP devices, and your manager doesn't natively understand each one.
That's where the MIB comes in.
You actually don't have to. The manufacturer of your device will supply you with a MIB file (usually a download from their website) that you'll load ("compile") into your SNMP manager. If you've ever installed a device driver on a PC, you understand this concept. Without the MIB for message translation, communication simply won't happen.
The fundamental purpose of the MIB is to translate numerical strings into human-readable text. When an SNMP device sends a Trap or other message, it identifies each data object in the message with a number string called an object identifier, or OID.
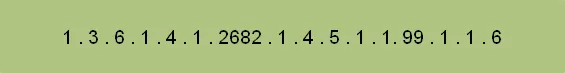
The MIB provides a text label called for each OID. Your SNMP manager uses the MIB as a codebook for translating the OID numbers into a human-readable display. Your manager needs the MIB in order to process messages from your devices. Without it, the message is just a meaningless string of numbers.
Your SNMP manager imports the MIB through a software function called compiling. Compiling converts the MIB from its raw ASCII format into a binary format the SNMP manager can use.
The MIB is really important because as far as SNMP managers and agents are concerned if a component of a network device isn't described in the MIB, it doesn't exist.
For example, imagine you have an SNMP RTU with a built-in temperature sensor. You think you'll get temperature alarms from this device - but you never do, no matter how hot it gets.
Why not? You read the RTU's MIB file and find out that it only lists discrete points and not the temperature sensor. Since the sensor isn't described in the MIB, the RTU can't send Traps with temperature data.
A MIB browser is a SNMP network management utility. In other words, it's a network management analysis mechanism that, through the SNMP protocol, can talk to various agents and devices on a computer network.
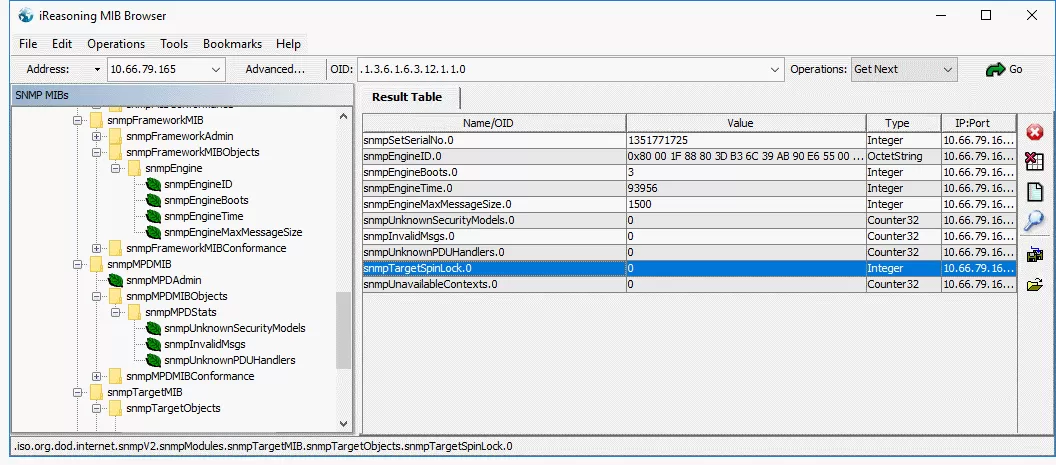
A good free MIB browser available is the iReasoning MIB browser (www.ireasoning.com). It has some limitations but should have the capabilities that most private users would need. Paid versions are also available to those who need no restrictions on the numbers of MIBs that are to be loaded while providing additional features.
A MIB browser is an invaluable utility for monitoring your SNMP devices and application, so having a good program is indispensable.
A MIB browser is an indispensable tool if you're trying to manage SNMP enabled devices because it can load standard and proprietary MIB files. This allows you to manipulate information available in an SNMP agent by browsing MIBs and performing other SNMP management actions.
Also, it doesn't matter who the manufacturer of your SNMP remote is. A combination of a packet analyzer and a MIB browser can help you troubleshoot a variety of network-related problems.
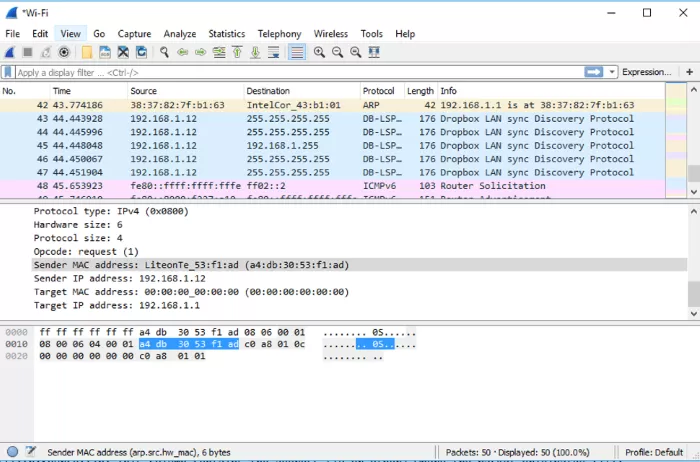
Wireshark is a network protocol analyzer and is available at no cost from www.wireshark.org. It's a free open-source utility that has found itself of use of many different people and is the recipient of many awards.
You can use it to capture, filter, and inspect network packets. It has features such as filters, color-coding, and plug-in support. Filters can be used to show only certain pieces of data while color-coding can make it easier for the user to read the data that is displayed on screen.
MIB browsers are incredibly valuable when performing SNMP agent comparisons. MIB browsers allow you to view and evaluate the MIB objects (like performance metrics, configuration settings, etc.) that each SNMP agent presents. The ability to compare SNMP agents helps validate the consistency of responses across different devices and facilitates compatibility checks, especially for legacy and modern devices, in SNMP monitoring setups.
Although you don't want to use a free SNMP manager in your network, it's a good idea to consider using other free tools such as the open-source Wireshark packet analyzer and the MIB browser from iReasoning since this combination makes troubleshooting accessible while also being cost-free.
There are several free SNMP browsers available for download that offer a range of features for managing and monitoring SNMP-enabled devices. Some of the popular options include:
An example of SNMP freeware is the ServersCheck MIB Browser. This Browser offers a user-friendly interface for browsing and managing SNMP MIB files. This makes it easy to navigate the hierarchical structure of MIB objects. The ServersCheck allows users to send SNMP Get, Set, and Trap commands directly from the browser. This aid in real-time monitoring and troubleshooting.
The browser supports SNMP versions v1, v2c, and v3. Supporting al three versions of the protocol sustains its wide compatibility. Advanced features include SNMP walk for automatic variable retrieval and a trap listener for real-time trap capture. These features provide comprehensive network health visibility and efficient device management.
Even if you're using a MIB browser, understanding MIBs and how they describe SNMP telemetry messaging is critical to maximizing your alarm system's capabilities.
The MIB is your best guide to the real capabilities of an SNMP device. Just looking at the physical components of a device won't tell you what kind of Traps you can get from it. You might think it's strange that a manufacturer would add a component to a device and not describe it in the MIB. However, the fact is that a lot of devices have sketchy MIBs that don't fully support all their functions.
One customer recently asked us about monitoring a new device, which was not in the library of SNMP MIBs for their system. They asked, "Can I reprogram the T/Mon to include this new device?" Fortunately, our T/Mon master station can integrate SNMP telemetry without needing to load or compile a MIB file or files.
For those with T/Mon monitoring systems, the MIB files can be a helpful reference when deciding how to monitor a new element in your network.
For those with older SNMP managers that require MIBs to be loaded in order to integrate SNMP messages from new network elements, MIB files are absolutely critical to understand. In some cases, you may even decide to edit them to improve the messages for your SNMP manager presentation.
The bottom line here is that when you're planning your SNMP monitoring and to get the best out of your SNMP MIB browser, you need to be able to read MIBs so you can have a realistic idea of what capabilities you have. When you're evaluating new SNMP equipment, examine its MIB file carefully before you purchase.
Our How to Read and Understand the SNMP MIB White Paper will help you understand why you absolutely need to be able to work with MIB files, especially if you're using an older SNMP manager.
In any case, you'll learn the essentials of SNMP MIB files and will probably agree that this white paper is a must-read for anyone who works with SNMP.

Morgana Siggins
Morgana Siggins is a marketing writer, content creator, and documentation specialist at DPS Telecom. She has created over 200 blog articles and videos sharing her years of experience in the remote monitoring industry.